5 Data Security Tips for Nonprofit Sponsorship Programs
Practical security steps for nonprofit sponsorship programs: RBAC, encryption and backups, data minimization, staff training, and incident response.

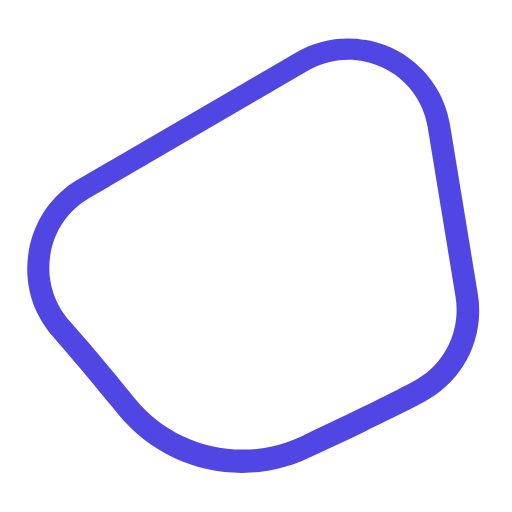
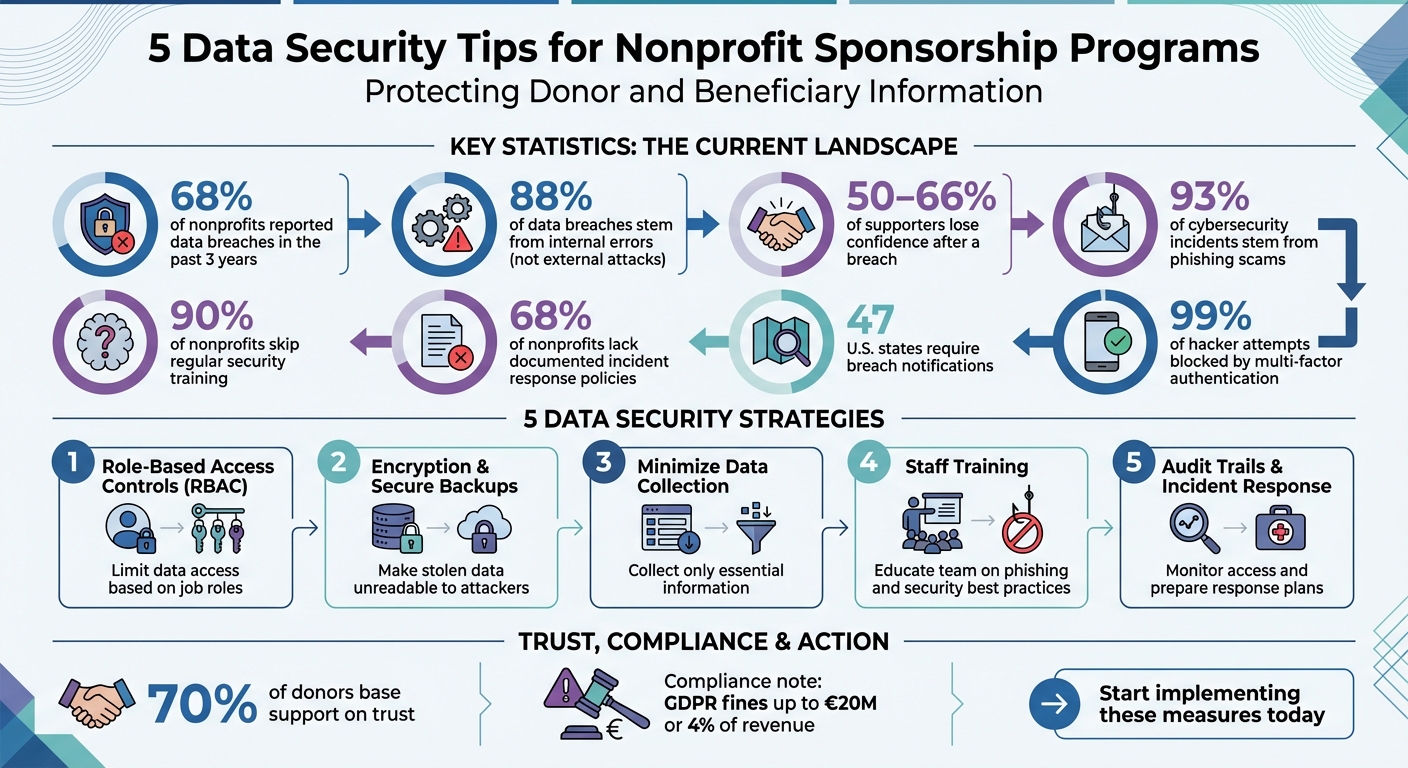
Nonprofit sponsorship programs handle highly sensitive data, from donor financial records to children’s personal details. A single data breach can erode trust and have severe financial, legal, and reputational consequences. With nonprofits being the second most targeted sector for cyberattacks and 68% reporting breaches in the past three years, securing your data is critical. Here are five actionable strategies to protect your organization:
- Role-Based Access Controls (RBAC): Limit data access based on job roles to reduce internal errors and comply with privacy laws.
- Encryption and Secure Backups: Encrypt sensitive data to make it unreadable to attackers and maintain secure backups for recovery.
- Minimize Data Collection: Only collect essential information to reduce exposure and simplify compliance.
- Staff Training: Educate your team on phishing scams, privacy policies, and ethical donor data management best practices to avoid internal mistakes.
- Audit Trails and Incident Response Plans: Monitor data access, detect issues early, and have a clear plan for responding to breaches.
Start implementing these measures today to safeguard sensitive information, comply with regulations, and maintain the trust of donors and beneficiaries.
Data Security Statistics for Nonprofit Organizations
Cybersecurity Best Practices for Charities and Nonprofits
1. Set Up Role-Based Access Controls
Role-based access controls (RBAC) allow you to manage data access in your sponsorship program based on specific job responsibilities. Instead of granting full access to your database, you assign permissions tailored to each role. For instance, your accounting team might need access to donation amounts and payment methods, while program managers focus on children's profiles and progress reports. This method minimizes unnecessary exposure to sensitive data, creating secure boundaries around critical information.
Restricting access also tackles a major issue: 88% of data breaches stem from internal errors rather than external attacks. For example, by limiting event volunteers to attendee lists and ensuring development staff can view giving histories without accessing detailed financial information, you strengthen your organization’s overall security and address common program challenges.
Protecting Donor and Child Information
RBAC helps shield your most sensitive data. By controlling who can access financial records and personal details - like credit card information or children's profiles - you significantly lower the risk of accidental exposure or misuse. These strict access controls are essential for maintaining the trust donors and families place in your organization.
Compliance with Privacy Regulations
In addition to safeguarding data, RBAC helps you stay compliant with privacy laws such as GDPR and CCPA. These regulations require that data access be limited to what’s necessary for specific tasks. With RBAC, staff can only access the information relevant to their roles, supporting your compliance efforts. During audits, clear access controls demonstrate your commitment to protecting data. Regularly reviewing and updating permissions - especially when employees change roles or leave - further strengthens your security framework.
Ease of Integration into Nonprofit Workflows
Adopting RBAC doesn’t have to disrupt your operations, especially when choosing the best child sponsorship software for your needs. Tools like HelpYouSponsor let administrators create "permission sets" to control access to specific settings, sponsorship programs, and donor profiles. This simplifies workflows and reduces administrative delays. To ensure success, document your access policies and train staff on best practices, such as using password managers for added security.
2. Encrypt Data and Create Secure Backups
While limiting access through roles helps reduce exposure, encryption adds another layer of defense by making any stolen data virtually useless.
Encryption works by turning your sponsorship data into unreadable code. This protects sensitive information like child profiles, donor details, and financial records - even if they’re stored in older formats like spreadsheets. If someone gains unauthorized access, all they’ll see is scrambled, indecipherable data.
Reducing the Risk of Data Breaches
Data breaches can seriously damage trust. Studies show that 50-66% of supporters lose confidence in an organization after a breach. Take the example of Broward Health: in January 2022, a ransomware attack exposed 1.35 million private records due to unauthorized network access. Encryption ensures that even if data is stolen, it’s useless without the proper decryption keys. Pairing encryption with multi-factor authentication (MFA) provides even stronger protection for your databases.
Meeting Privacy Standards and Regulations
Encryption isn’t just about security - it’s also about compliance. Many U.S. states reduce breach notification requirements if encrypted data is stolen, helping organizations avoid unnecessary fallout. On a global scale, regulations like GDPR impose steep penalties - up to €20 million or 4% of annual revenue - for failing to protect data properly. Encryption helps you stay on the right side of these rules.
Easy Integration for Nonprofits
Cutting-edge platforms, such as HelpYouSponsor, offer bank-grade encryption and automated backups, making it easier for smaller nonprofits to secure their data without needing technical expertise. Similarly, cloud storage solutions provide advanced security features and disaster recovery options, so you can quickly restore vital records in the event of an attack or system failure.
3. Collect Only the Data You Need
The idea here is straightforward: the less data you collect, the less you have to protect. Every extra piece of information you store increases your exposure. If a breach happens, hackers can only access the data you've gathered - so limiting what you collect from the start is a smart way to reduce risk. This concept sets the foundation for protecting sensitive donor and beneficiary information.
Protecting Vulnerable Beneficiaries and Donors
Sponsorship programs often handle highly sensitive details, like children's health records, school information, or even their locations. Trust is everything in these programs, and a data leak can quickly shatter it. By limiting the amount of sensitive information accessible to staff and volunteers, you can significantly reduce the chances of accidental exposure.
Simplifying Compliance and Limiting Breach Consequences
When you only collect what’s necessary, staying compliant with data regulations becomes easier. You can focus your resources on safeguarding critical information - such as names, email addresses, and donation histories - instead of worrying about unnecessary details like Social Security numbers or birth dates.
For instance, in 2022, The Nature Conservancy made a bold move by reducing the fields on its donor forms from 15 to 8, eliminating requests for birth dates. This change paid off: they saw a 30% increase in form completions and a 25% reduction in privacy complaints.
As Data Officer Sarah Johnson explained, "By asking for less, we actually got more useful data and happier donors".
How to Minimize Data Collection
Start with an audit of your forms. Identify and remove fields that aren’t essential or pose unnecessary risks. Replace open text fields with dropdown menus to standardize responses and avoid gathering irrelevant details. Use anonymous surveys for assessments to keep responses separate from donor profiles. Platforms like HelpYouSponsor can make this process easier by offering role-based access controls, ensuring that even the necessary data is only accessible to the right people. These steps, combined with other security measures, can strengthen your overall approach to data protection.
4. Train Staff on Privacy and Security Practices
It's shocking but true: 88% of breaches are tied to internal mistakes, and 90% of nonprofits skip regular training. Even the most well-meaning staff can unintentionally put sensitive donor and child information at risk without proper guidance.
Prevention
Did you know that 93% of cybersecurity incidents in nonprofits stem from phishing scams? Many attacks start with something as simple as clicking a suspicious link or replying to a fraudulent email. That’s why training your team to recognize warning signs is critical. Teach them to look out for red flags like:
- Urgent requests for personal data
- Emails from unfamiliar senders
- Suspicious or shortened links
Take it a step further by running simulated phishing exercises every quarter. These simulations give your staff hands-on experience spotting threats in a controlled environment.
Don't forget basic physical security measures, too. Encourage habits like locking computers when unattended, securing paper records, and using privacy screens. Once your team knows what to watch for, weave these practices into their daily routines for lasting impact.
To make training stick, start with a solid onboarding session. Cover essentials like your privacy policies, password best practices, and how to report security concerns. Then, follow up with quarterly refreshers - just 15 to 20 minutes long - to update staff on the latest phishing tactics and recent breaches. Tailor the training to fit each role. For instance:
- Marketing teams should understand CAN-SPAM regulations.
- Fundraising staff need to focus on donor privacy rights and HIPAA requirements.
Lastly, create a safe, non-punitive environment for reporting suspicious activity. When people feel comfortable coming forward, issues can be addressed before they escalate.
Staying Compliant and Reducing Risk
Regular training doesn’t just protect your data - it ensures your nonprofit stays aligned with privacy laws like GDPR, HIPAA, and CCPA. When staff understand their responsibilities, compliance becomes second nature rather than just another task to check off.
Tools like HelpYouSponsor make this easier by offering role-based access controls (RBAC), so employees only see the data they need to do their jobs. Combine this with encryption and other technical safeguards, and you’ve got a strong defense. Together, these measures protect the vulnerable children and generous donors who place their trust in your organization.
5. Keep Audit Trails and Prepare Incident Response Plans
A staggering 68% of nonprofits lack documented policies for responding to cyberattacks. This means that when a breach occurs, many organizations are left scrambling without a clear course of action. By combining audit trails with incident response plans, nonprofits can detect issues early and act swiftly to minimize harm.
Protecting Donor and Child Information
Think of audit trails as the digital equivalent of security cameras - they monitor who accesses sensitive information, like donor records or vulnerable children's data. If someone accesses information they shouldn’t, you’ll know immediately. Pair this with a solid incident response plan, and you can quickly contain any damage before it escalates.
Compliance with Privacy Regulations
47 U.S. states require nonprofits to notify individuals if their personal information is exposed in a breach. Without a clear response plan, fulfilling these legal requirements can be chaotic. Regulations like GDPR take it further, requiring breach notifications within 72 hours and imposing fines that can reach €20 million or 4% of annual revenue for non-compliance.
To meet these demands, your incident response plan should assign clear roles, such as an Incident Response Lead, IT Forensics Specialist, and Legal Advisor. When everyone knows their responsibilities ahead of time, you’ll be better equipped to meet tight deadlines and avoid penalties. Incorporating audit trails into your daily operations also strengthens compliance without adding unnecessary complexity.
Ease of Integration into Nonprofit Workflows
Here’s the good news: implementing these safeguards doesn’t have to disrupt your operations. Tools like HelpYouSponsor offer role-based access controls that automatically log who views donor or child information, creating audit trails without adding extra work for your team. Conducting quarterly audits ensures that only authorized personnel access sensitive data.
This proactive approach aligns with your broader commitment to protecting donor and child information, reinforcing trust and security at every level.
As Cisco explains: "An incident response plan is a set of instructions to help IT staff detect, respond to, and recover from network security incidents. These types of plans address issues like cybercrime, data loss, and service outages that threaten daily work".
Conclusion
Data security is the backbone of nonprofit sponsorship programs. Safeguarding donor and child information isn’t just about meeting legal requirements - it’s about earning and keeping the trust that fuels your mission. With nearly 70% of donors basing their support on trust, a single breach can have lasting consequences for your organization’s reputation and donor relationships.
The five strategies outlined - role-based access controls, encryption and backups, data minimization, staff training, and audit trails with incident response plans - offer a strong framework for protecting sensitive information. Considering that most breaches result from internal errors, these steps directly address the areas where nonprofits are most vulnerable. Additionally, they ensure compliance with key regulations like PCI DSS, GDPR, CCPA, and various state-specific laws.
Taking action now is critical. Start by implementing multi-factor authentication, which blocks 99% of hacker attempts. Schedule your first security audit and develop a clear incident response plan to further reduce risks. Every proactive measure you take reinforces your organization’s commitment to ethical data management.
The benefits go far beyond avoiding breaches. Transparency in handling data builds donor confidence - 95% of donors are more likely to trust organizations with high levels of transparency. By consistently applying these practices, you not only protect sensitive information but also strengthen relationships with supporters, turning them into lifelong advocates for your cause.
"Protecting donor privacy isn't just about preventing breaches - it's about maintaining the trust that fuels your organization." - HelpYouSponsor
FAQs
What donor and child data is safest to collect?
When it comes to collecting data, focus on information that’s necessary and manageable. This typically includes personal details like names, addresses, payment information, donation history, and child profiles. To keep this data safe, implement strong security measures such as encryption, role-based access controls, and ensure compliance with privacy laws like GDPR and CCPA. Protecting sensitive information isn’t just about following regulations - it’s also about maintaining trust with those who share their data with you.
How do we set RBAC roles in a sponsorship program?
To implement RBAC, start by assigning permissions based on the specific job functions within your organization. Create roles such as administrators, fundraisers, or data managers, and clearly define the level of access each role requires - whether it's viewing, editing, or deleting data. Once roles are defined, assign users to the appropriate roles based on their responsibilities.
By integrating these roles into your system, you can maintain strong data security and meet compliance requirements. This method helps protect sensitive donor and child information while ensuring only authorized individuals have access to the data they need.
What should an incident response plan include for nonprofits?
An effective incident response plan for nonprofits is crucial for tackling cybersecurity threats. It should clearly define steps to identify, contain, eradicate, and recover from such incidents. Equally important, the plan must include well-structured communication protocols to notify stakeholders who may be affected. This ensures transparency and compliance with any legal obligations.
Given the sensitive nature of nonprofit operations, special attention should be given to safeguarding donor information and data related to children. Protecting these details not only preserves trust but also upholds ethical and legal responsibilities.